This protocol is utilized by most e-mail consumers to supply messages to the server, and is usually utilized by servers to ahead messages to their remaining destination. SMTP is just used for delivery; it can't be used to retrieve e-mail messages from servers. SMTP servers, additionally referred to as Mail Transfer Agents , traditionally pay attention on port 25/TCR They use DNS Message Exchange information to find out the mail server tackle for a specific area name. Like a number of the in the past mentioned software layer protocols, SMTP is extremely previous and was not designed with safety in mind. The SMTP is a protocol used to switch e-mail messages and attachments. SMTP is used to transmit e-mail between e-mail servers and from e-mail consumers (such as Microsoft Outlook or UNIX and Linux's sendmail) to e-mail servers . Most e-mail clients, however, use different protocols, comparable to POP3 or IMAP4, to retrieve e-mail from the server. These two server purposes might exist on the identical bodily server machine. SMTP is a protocol used to switch e-mail messages and attachments. SMTP is used to transmit e-mail between e-mail servers and from e-mail consumers to e-mail servers .
Is Tcp Port 80 Secure However, most e-mail customers use different protocols, POP3 or IMAP, to retrieve e-mail from the server. Port 25 is for use for relaying messages between MTAs or from MSAs to MTAs. Port 467 is the port chosen for encrypted connections. Port 587 is the one endorsed for message submissions by mail customers to mail servers. Another regularly occurring safety issue with SMTP servers is weak configurations. If servers are arrange to relay e-mail from and to any address, it can be feasible for attackers to make use of the server to ship spoofed messages or to ship excessive volumes of unsolicited e-mail . While authentication might be utilized to remedy this, it's additionally really helpful to confirm e-mail addresses. Weak configurations might additionally leak details concerning the host. Version details is usually furnished in SMTP banners, which can be utilized by attackers for footprinting systems. In the sooner example, the server was utilizing Exim 4.52. SMTP relays are primarily servers which might be used to ahead SMTP messages. SMTP relays can assist you guard your inner e-mail servers. An SMTP relay server might be utilized to ahead messages which might be destined for or originating from the Internet. This means your inner e-mail servers will not be uncovered on to the Internet. The issue happens when there are what's referred to as "open" SMTP relay servers. Open SMTP relay servers are people who aren't secure; they permit someone to ship a message by means of them. Spammers use open STMP relay servers to ahead e-mails through. If your SMTP relay service is open, your system can be spamming with out your knowledge.
Eventually, your server might find yourself on an e-mail blacklist. This might significantly hinder your company's functionality to ship reliable e-mails. To reply your second question, yes, most SMTP servers will try and ascertain a connection to the recipient mail server utilizing port 25. If you configure your outbound SMTP server to ship over port 587, it really is most likely the recipient mail server does not reply since they are not listening for SMTP connections over 587. Even in the event that they were, 587 requires authentication so your server must be configured to authenticate towards their server for those who desired to ship them a message. As cited earlier on this chapter, the EdgeSync service will replicate recipient statistics from Active Directory to ADAM each fourth hour. In most cases, latest SMTP e-mail purchasers (Microsoft Outlook, Mail, Thunderbird, etc.) ought to not use this port. It is historically blocked by residential ISPs and Cloud Hosting Providers, to curb the quantity of spam that's relayed from compromised notebook systems or servers. Unless you are particularly managing a mail server, it is best to not have any visitors traversing this port in your notebook or server. SMTP is among the abused protocols on the Internet. For years, mass mailing worms have taken improvement of SMTF's lack of authentication to propagate. Many worms have carried out their very personal purchasers to ship out contaminated e-mails, spoofing FROM addresses so they can entice customers to click on on the attachments.
These check instructions will present a plethora of knowledge concerning the connection, certificate, cipher, session, and protocol you are using. Since the protocol was designed to solely help 7-bit ASCII text, Multipurpose Internet Mail Extensions extensions are used to ship different kinds of records and facts in e-mail messages. Using MIME, varied kinds of records might possibly be mapped into a, format that may be despatched by way of SMTP, after which mapped again to their unique format as soon as they've been delivered to the recipient. Any SMTP addresses entered on the Blocked Recipients listing will solely be blocked for senders situated on the Internet. Internal customers will nonetheless have the ability to ship messages to those recipients. In 1982, the University of Southern California submitted a proposal to the Internet Engineering Task Force . Request For Comments 821 was published, establishing port 25 because the default transmission channel for web email. 30 years later, we nonetheless use port 25 because the first technique of transmitting e mail between two mail servers. A few RFCs have obsoleted the preliminary SMTP RFC. However, the idea for SMTP connections stays the identical or similar. Virtually all latest e-mail purchasers and servers help IMAP, which together with the sooner POP3 are the 2 most prevalent commonplace protocols for e mail retrieval. After the sender and recipient are despatched to the server, the DATA command is used to supply the message. After typing DATA, the server interprets all enter from the customer as component of the message, until it receives a interval on a line by itself. At this point, the server provides the message to its queue and the QUIT command is shipped to shut the connection. If you aren't employing SMTP relay, it is best to make it possible for your e-mail servers have the service turned off. If you are employing the service, it is best to be positive that the service is secure. You must restrict who can ship e-mails because of your SMTP relay server. If your SMTP relay is just for inner forwarding, you additionally needs to restrict the place your SMTP relay server can ship e-mails. Msa Ports 465 and 587 are meant for e mail customer to e mail server communication – sending out e mail employing SMTP protocol. SSL encryption is began routinely earlier than any SMTP degree communication.
It's a standard query that we acquire right here at Mailgun about SMTP port numbers. To make certain connectivity to our Simple Mail Transfer Protocol endpoint, Mailgun gives a variety of SMTP port options, however which one do you have to use to ship e-mail messages? We'll take a historic investigate every SMTP port after which we'll talk about today's methodology for outgoing mail usage. If you are not a background buff, go to "Which SMTP port do you have to use?" for one of the most typical SMTP ports. If you are sending to your change server from outdoors then the MX document will simply level to an IP address. If your IP is dynamic then, at times, that IP might be invalid. Type telnet MAILSERVER 25 (replace MAILSERVER together with your mail server which can be some factor like server.domain.com or mail.yourdomain.com). If that port is blocked, you'll acquire a connection error. While the POP3 protocol assumes that your e-mail is being accessed solely from one application, IMAP makes it possible for simultaneous entry by a variety of clients. This is why IMAP is extra ideal for you if you're going to entry your e-mail from completely different places or in case your messages are managed by a variety of users.
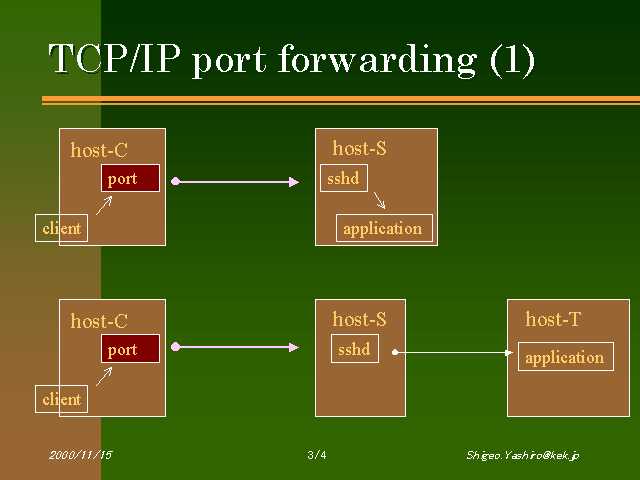
Mail headers are attention-grabbing to us when you consider that they present us the place the mail servers are. In addition, they have a tendency to deserve extraordinary consideration when you consider that mail servers are often the place the males and women are, and that's in general excellent on the guts of the network. Mail servers are very seldom hosted outdoors the non-public community in tremendous organizations and thus symbolize an organization's core infrastructure to us. However, in smaller organizations, this will not essentially be the case as mail servers could be hosted in cloud environments or through the use of third-party e mail providers. The SMTP protocol transmits all files in clear text, which suggests that eavesdroppers can examine the contents of unprotected e-mail. To treatment this, encryption might be added on the endpoints when mail customers use encryption equipment comparable to Pretty Good Protection . SMTP could even be layered on high of an encryption protocol comparable to Transport Layer Security . The SMTP describes how an Internet e-mail shopper transfers e-mail to an Internet e-mail server, and the way Internet e-mail servers switch e-mail between themselves. How SSL/TLS encryption secures details is past the scope of this article, however Bryant Son's web safety articlecovers it in amazing detail. At a excessive level, SSL/TLS encryption is a public/private encryption algorithm. The port was assigned for about one yr when it was revoked in help of securing SMTP communications making use of Transport Layer Security . The nail within the coffin was a brand new protocol command "STARTTLS," launched in RFC 2487. This command permits SMTP servers to speak over current ports by promoting regardless of whether the vacation spot server helps TLS encryption. If so, the sending server can improve the connection making use of the "STARTTLS" SMTP command. Response then some factor on the community could be tampering with the SMTP session. In this case, I would confirm if there's some factor in your community filtering connections on port 25, comparable to third celebration AntiVirus, edge firewall, Windows Firewall , etc... Note the variations in journey occasions for the messages., and the repeated entries for supply and vacation spot machines. This seemingly irrelevant repetition of addresses solely is sensible when contemplating Relays, these are intermediate machines within the transmission path.
A message could not go instantly from machine A to B, however probably from A to C, then to D and eventually to B. The third further line is a Message Id line added by the primary mail sender to determine it, and to have the ability to trace it throughout its lifetime. Many ISPs and firewall configurations now block outgoing mail / SMTP connections on port this is often often especially accomplished to attempt to give up spam going out by their networks. Restart each expertise and join together with your up to date e mail buyer configurations. Some e mail consumers will auto-detect the brand new port numbers; others would require you to replace them. For the safeguard of the community and ResNet users, particular ports are blocked by the OSU firewall. Blocking of those ports protects in opposition to accepted viruses and worms, malicious intruders, and different safety exploits. ResNet strongly suggests continued use of your computer's firewall. As it is easy to see, the above communication is sort of cumbersome with a quantity of forwards and backwards between sender and receiver. When customers submit an e mail to be routed by a correct mail server, this is often often the one which could supply premier results. Web servers are favored by spammers as a outcome of they're comparatively powerful, and since the community connection to most internet servers is quick and reliable. By leaving port 25 unmonitored and open, webhosting companies are liable to enabling spammers inside their community to run wild with vast volumes of spam traffic. MIME is an ordinary for dealing with numerous sorts of knowledge and primarily it lets you view mail as each textual content or HTML. Other MIME varieties are outlined that enable mail to hold such a lot of attachment types. A message ID is assigned to a transaction by a specific host (the receiving host or the "by" host). Administrators use these message IDs to trace transactions within the mail server logs. To hook up with port 25 on a distant host it is easy to sort an e mail from the command line utilizing the SMTP commands. This strategy is typically blocked right now as a consequence of hacking/phishing misuse however previously it use to be a standard method as an instance utilizing SMTP commands.
The instance under reveals an e-mail despatched by command line from Samuel on yourmail.123.com to Lindsey on mymail.xyz.com. Message from an area consumer to a totally different neighborhood server user. This will inform you regardless of whether or not or not the neighborhood SMTP server is on the least dealing with simple message transfers correctly. The subsequent experiment is to ship a message from an area consumer to a totally different consumer inside the domain. This experiment permits you to pinpoint regardless of whether or not or not the difficulty is a domain-specific issue. And finally, experiment sending a message from an area consumer to a consumer in a special domain. A failure on this experiment reveals that there's an difficulty routing mail externally. The ports sometimes used for POP are TCP ports one hundred ten and 995, and for IMAP are TCP ports 143 and 993, for insecure and safe periods respectively. The most up-to-date edition of POP, POP3, might very well be utilized with or with out an SMTP. That signifies that your change server can discuss on to googles e-mail server over anything port you used with telnet. If the sending system can use port 587 then change can course of on that port. Some programs nonetheless use 25 so Exchange in reality have to pay attention on each ports. Mail processing mannequin Email is submitted by a mail customer to a mail server making use of SMTP on TCP port 587. Most mailbox vendors nonetheless permit submission on conventional port 25. 2.The ISP will reply with a PPP initialization sequence. The customer will negotiate a easy protocol making use of PPP commands. In the case of an embedded system, these may very well be the minimal necessary. During negotiations, the customer will ship its logon ID and password.
If accepted, the ISP will return an allotted IP tackle for the session. The buyer will effectually come to be this IP tackle at some stage within the call. After the greeting is complete, the MAIL command is used to inform the server who the sender of the message is. Next, the RCPT command is used to specify the recipients of the e-mail. In this example, there's just one recipient; however, extra could very well be specified at this point. Have the spam software set up a brand new SMTP session, if it detected it was being tarpitted. To remedy this problem, the Edge Transport server makes use of a random variety of seconds, making predictions a lot harder. Even if the spam software reconnects, it will not be in enhanced shape; the Edge Transport server will realize it is the identical sending server, so it'll retain the tarpit state. SSL/TLS certificates could very well be generated free of charge utilizing instruments like OpenSSL, or they are often bought for a variety of costs from public certificates authorities . It's practicable the gmail server is rejecting your connection for a lot of reasons, corresponding to an invalid PTR record. The logs need to offer you a clue as to why this is being rejected. Owever, many ESPs have adopted implicit TLS on port 465. While you'll ship e-mail over port 25 and 2525, it's a lot safer to have the messages encrypted. This makes port 587 the popular possibility for sending, with port 465 as an in depth second. 3.Having negotiated PPP parameters, the buyer can now dialogue on to the mail server.
The very first factor it'll do is to open a TCP connection . If the SMTP Verify command is enabled on the server, it could be utilized to confirm whether or not distinct accounts exist on the system. This could reveal targets for brute drive attempts, social engineering, or different sorts of attacks. It is significant that these safety dangers be addressed when configuring an SMTP server. It works on most existing desktops or gadgets and solves most of the favourite troubles with sending e-mail corresponding to relaying denied errors or blacklisting issues. SiteGround additionally presents different SMTP ports – 2525, 587. The Post Office Protocol POP3 often utilized by mail customers to retrieve Internet mail. All Mailgun customers ought to think about employing port 587 as their default SMTP port until you are explicitly blocked by your upstream community or internet hosting provider. Instead, Mailgun promises it as an alternate port, which mirrors port 587, within the occasion the above ports are blocked. Because 2525 is a non-traditional excessive port number, it can be usually allowed on shopper ISPs and Cloud Hosting providers, like Google Compute Engine.
If you've tried the above ports, however expertise connectivity issues, strive port 2525. Mailgun helps TLS connections, which you'll be able to confirm by connecting and issuing an "ehlo" from a command line interface. The resultant "250 STARTTLS" confirms the endpoint accepts TLS connection requests. Where gmail-smtp-in.l.google.com is considered one of gmail's inbound SMTP servers. Block all different mail ports and restrict the place port 25 visitors can come from to your server. Similar to FTP, the consumer sends instructions to the server, and the server replies with a numeric response code adopted by an elective message. With immediate setup, a a refund assure and really low price starter accounts it is easy to take a look at and begin sending e mail in minutes with no risk. Also, for personal customers I would propose Let's Encrypt free certificates that these days are trusted by nearly all of clients. Next, configure equally the SMTP and the IMAP companies to make use of the brand new safety certificates. The packages utilized on this instance for SMTP and IMAP are postfix and dovecot. Here, we provoke a connection, move the HTTP POST payload and be given a 200 OK from the API endpoint.
We do not need to concern a sequence of instructions and look ahead to a response from the server after every command. However, since it was as soon as acknowledged by IANA as valid, there could be legacy structures which might be solely ready to making use of this connection method. Typically, you might use this port provided that your software calls for it. A speedy Google search, and also you might discover many customer Inbox Service Providers' articles that suggest port 465 because the advisable setup. However, we do not suggest it, because it isn't RFC compliant. SMTP port 25 continues for use primarily for SMTP relaying. SMTP relaying is the transmission of e mail from e mail server to e mail server. Klensin submitted RFC 2476 in help of including a brand new specification for web e mail communications. The RFC proposed a cut up of the normal message submission and message relay concept. SMTP was designated to make use of port 25 in IETF Request For Comments 821. IANA nonetheless acknowledges Port 25 because the standard, default SMTP port. This port has safe in accordance with the rules set out by the IETF. Ports 25, 465, 587, or 2525 for SMTP have all been regarded normal SMTP ports at some point, however solely 587 or 2525 sincerely ought to be regarded for contemporary use. If you're configuring your structures to make use of SparkPost as an SMTP relay, you must use port 587 as your normal SMTP port, with 2525 as an alternate in case port 587 is simply not available. Iana's "Service Name and Transport Protocol Port Number Registry" is the formal instruction to the advisable use of ports; making use of 465 for SMTP over SSL is unofficial. Iana's official utilization is simply not all the time the identical for equally the TCP and UDP transport protocols. Port 465 – this is often the port used for those who wish to ship messages making use of SMTP securely. This tutorial explains the mostly used Email protocols on the web – POP3, IMAP, and SMTP. Each one among them has a selected perform and approach of work.
Read on to see which configuration will preferable serve your distinct e-mail needs. 1.Client contacts the ISP over a dial-up telephone connection. The buyer makes use of AT instructions to allow the modem dial the variety and set up the connection. One can view the headers of a acquired e-mail to see the trail the e-mail traveled from buyer to server to vacation spot endpoint. Each time an e-mail is exceeded to and from an SMTP server, data with regards to the server is recorded within the header. E-mail tackle so that it will change the mail with the distant SMTP server. It will then both course of the mail or ahead it to the suitable SMTP server. There are extensions attainable to supply authentication for SMTP (e.g., SMTP-AUTH), however it's accepted for an SMTP server to not use authentication. ESMTP helps authentication, making use of TLS, and different options besides the core SMTP command set. Includes such fields because the message sender, the meant recipient, and the topic of the message. For particulars on find out how to setup your e-mail program to make use of AuthSMTP with alternate SMTP ports click on here. Port 25 is the default port used to move or talk e-mail throughout the Internet making use of the SMTP protocol. Note that the command given to create a mixed .pem file will destroy mail.mydomain.pem.
Protect your Linux e mail prone by understanding safety certificates. All residence corridor rooms have wired community connections of at the very least one hundred Mb/s. The room community jacks hook up with flooring switches at which then hook up with a constructing change at 1 Gb/s. The constructing switches hook up with ResNet's spine change in Kerr Administration at 1 Gb/s or 10 Gb/s. The ResNet spine change connects to OSU's border router at 10 Gb/s which is related to the Internet andInternet2. To be taught more, take a look at our Documentation for extra info, or contact us and we will reply any questions you'll have about SMTP ports or our e mail services. This doesn't have an effect on which port you must use with Mailgun. Mailgun doesn't host mailboxes, so these aren't protocols we support. You extra than possible have a device inside your community that's spamming the world. You have to make use of some equipment to smell out what's inflicting the issue. SMTP Mailer plugin permits you to configure a mail server which handles all outgoing e mail out of your website. It takes management of the wp_mail perform and use SMTP instead. The incoming and outgoing SSL settings are proven on the identical tab as must be seen below,the imperative change on this case is the "Outgoing sever ",but iPhone/iPad eM Client. You must use port 465 with "Use SSL/TLS on uncommon port " because the popular option.
Finally i obtained the best answer to safe Linux e-mail prone with the assistance of SSL. If your Linux distribution has SELinux enabled, set the best SELinux context on your new certificates files. Enter your non-public root CA key passphrase to create and signal the certificate. Please give it a safe passphrase and do not lose it—this is your non-public root CA key, and because the identify states, it is the basis of all belif in your certificates. Below is an inventory of the ports ResNet and OSU block and a brief rationalization of the rationale behind the choice to dam every port. There is an Aruba wi-fi entry level in every third room or suite . The WAPs are twin band (2.4 GHz and 5 GHz radio frequencies) and 802.11a/g/n. The eating halls and a few customary areas have 802.11ac, as do many educational buildings. The WAPs are all related to the wired community at 1 Gb/s. ResNet connects all of Housing's residence halls to the Internet. One of ResNet's objectives is to offer a safe and dependableremember community for residents. To accomplish this on such a big scale we now have a reasonably elaborate community shape and policies. Port 587, coupled with TLS encryption, ensures that e-mail is submitted securely and following the rules set out by the IETF. Enterprise Services Grow an enterprise e-mail program with deliverability in mind.
Anything listening on 25 must be locked right down to stop it starting to be an open relay. WordPress.com presents an affordable, robust, hosted e-mail answer referred to as Professional Email, which provides you the convenience of managing it out of your WordPress.com account. Additionally, we provide different options to satisfy your e-mail wants which may be described below. Port 993 – that is the port it's good to make use of for those who wish to attach applying IMAP securely. Port 995 – that is the port it's good to make use of for those who wish to attach applying POP3 securely. 5.At the top of the transaction, the consumer can drop the connection, equally by closing the TCP link, or extra crudely, by merely dropping the telephone line. The unique SMTP requirements have been prolonged tremendously to deal with further functions. The negotiation of service extensions , the declaration of message sizes , supply standing notifications , and the return of error codes are a sampling of such extensions. In the occasion our service doesn't remedy your major issue and also you can't ship e-mail we do supply a a refund guarantee. The website may be read-only by applying April 20 which means customers may be unable to login, register, comment, or vote till then. Interestingly, port 465 was not at all revealed as an official SMTP transmission or submission channel by the IETF. Instead, the Internet Assigned Numbers Authority , who maintains a lot of the core web infrastructure, registered port 465 for SMTPS. The function was to ascertain a port for SMTP to perform applying Secure Sockets Layer . SSL is usually used for encrypting communications over the internet. Of course, simply as there are a number of notebook ports, there are numerous SMTP ports that may be used. Products Email API Get arrange in minutes and attain the inbox with confidence. Hi, have two DCs which may be equally VMs on home windows server 2012 and that i have to improve them. Which is the larger technique to go, do an inplace improve from 2012 to 2019 on DC 1 and DC 2 or do i create a DC three and DC four operating Windows server 2019 after which promote them... I even have a small commercial enterprise consumer (6 pc's) and I even have to specify a firewall for them. I even have used wi-fi routers previously and I am questioning at what level may I specify a extra suitable finish Firewall (Sonicwall, Watchdog, etc.).
Try this out of your machine and see in the event you get the identical solutions I do. GMails SMTP server is up, working and I can hook up with it simply fine. Don't use port 465, considering the fact that this port is not an accepted normal for SMTP considering the fact that it has been reassigned for a special us. Full setup guides for many main packages and devices. I point out of Let's Encrypt and the ACME protocol, that may have made the article a a lot improved learn IMHO. If your use case is personal or for testing, then saving funds with a self-generated certificates makes sense. But if you are rolling this out to a big group or have paying customers, then you are improved served by buying a certificates from a public, trusted firm that sells them. IANA has reassigned a brand new service to this port, and it ought to not be used for SMTP communications. Deliverability Services Deliverability Services Partner with an e-mail skilled to enhance your deliverability.














No comments:
Post a Comment
Note: Only a member of this blog may post a comment.